How to Add Another KeyControl Security Admin From Active Directory
This post will show how to add another Security Admin to Entrust KeyControl from Active Directory.

To get started here is what you will need to complete the steps in this post:
- A deployed Entrust KeyControl v5.4 cluster connected to Active Directory (Click this sentence to learn how to do this)
- Active Directory account info to be added
Now, let’s get started…
Add a Second KeyControl Security Administrator from Active Directory
-
Click Security from the menu bar then click the blue Actions button and select Create User
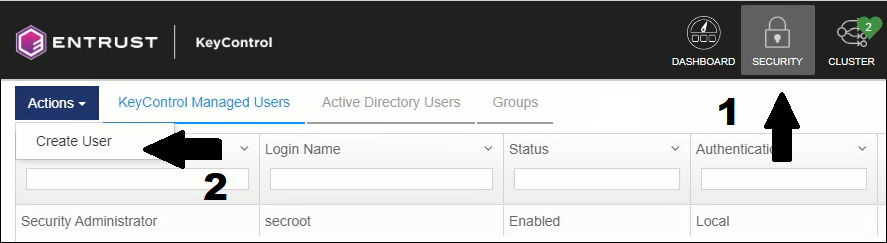
Create User
-
Complete the required fields on this form and click Next
NOTE: The Login Name field should match the username in Active Directory
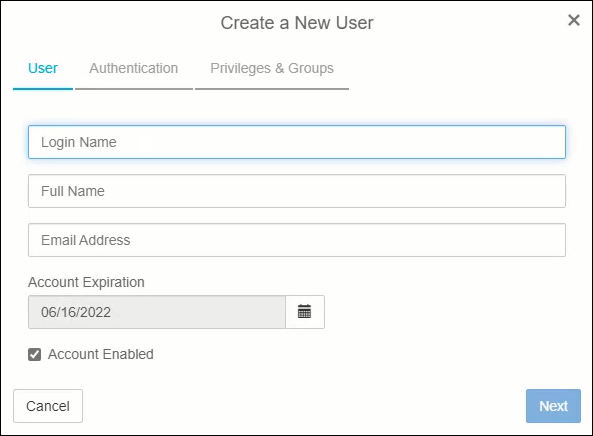
User details
-
Click Next on this dialog since we are adding a new user from Active Directory.
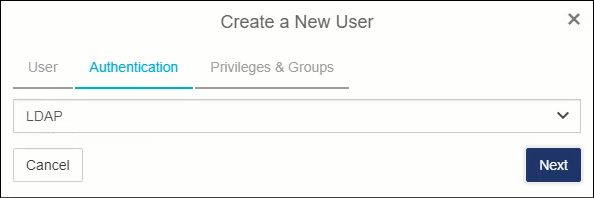
Authentication type
-
We are adding a second KeyControl Security Admin to mimic the built-in secroot account. So, you should select all of the admin types:
- Security Admin
- Domain Admin
- Cloud Admin
Make sure the default Cloud Admin Group has also been moved to the assigned groups section. Click Create when you are ready.
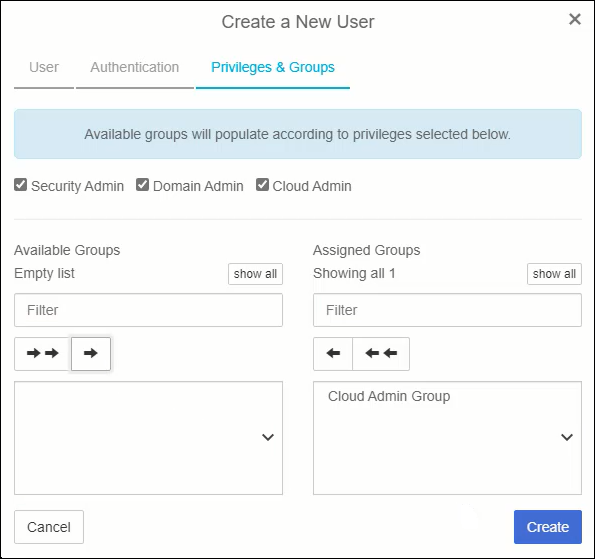
Privileges & Groups
-
After clicking the create button you will be prompted to download the Admin key.
NOTE: This Admin Key replaces the original Admin Key that was generated when the KeyControl cluster was first created.
This Admin Key only pertains to the newly created Security Admin you just created. The secroot user also has a new Admin Key. If you configured email notifications when creating the cluster then it will automatically be emailed to the secroot user. Click Download on this dialog and store the Admin Key in a safe place.
It is crucial that each Security Admin safely stores their copy of the latest generation of the Admin Key and knows where it is during times when the Admin Key is required. More on this later.
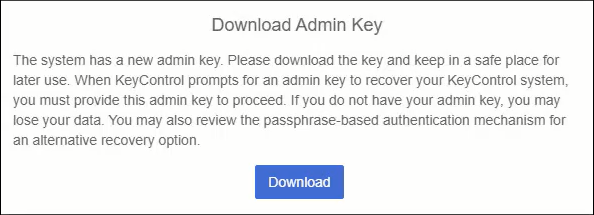
Download Admin Key
Congratulatins! You have successfully created a new Security Administrator from Active Directory.
Summary
This post walked through the process of adding a second KeyControl Security Administrator from Active Directory. This provides another way to administer KeyControl. It also enables your organization to follow the usual IT process of managing all of your accounts through a centralized user directory such as Active Directory.
In a follow-on post, I will write about how to add a KeyControl v5.4 (KMS) cluster as Key Provider in vCenter 7.x.
Related Posts
Here are links to related posts:
- Register for a 30-day trial of Entrust KeyControl
- How to deploy a 2-node Entrust KeyControl v5.4 cluster
- How to Connect Entrust KeyControl v5.4 to Active Directory
- How to Add a Another Security Admin to Entrust KeyControl v5.4 from Active Directory
- How to Add KeyControl v5.4 as a Key Provider in VSphere 7
- Entrust KeyControl YouTube playlist
- YouTube video: Entrust KeyControl - Joining a KMS Cluster to Active Directory
If there is something you think I’m missing and feel should be added, please let me know.
Thanks for reading!